A lesson learned from Uber and Reddit Security Incident
MFA is becoming increasingly popular as a means of combating rising identity theft through phishing and becoming compliant with identity and access management regulations. MFA has proved to be a simple but effective security control to reduce the risk of your organization.
However, recent security incidents on Reddit and Uber, on the other hand, demonstrate MFA’s limitations. Furthermore, while participating in some security group discussions, I discovered that some security engineers are not fully aware of these limitations, which could jeopardize your organization regardless of whether you are using a third-party MFA or implementing your own MFA. In this article, we will attempt to detail the most common limitations of MFA that people have overlooked.
Some Limitation about MFA
Here are some MFA drawbacks that are frequently encountered.
MFA could reduce phishing attacks significantly, but could not eliminate them
MFA could be bypass even for the matured vendors
Misconfiguration and poor implementation may make your MFA useless
Email and SMS based MFA are not as secure as you expected
Limitation 1: MFA will NOT eliminate successful phishing attack
MFA makes it more difficult for hackers to gain access to networks and information systems if passwords or personal identification numbers (PINs) are compromised through phishing attacks or other means because MFA adds multiple factors , such as OTP, SMS Code, App PUSH, for authentication besides the password and PINS. Because of this, many security administrators disregard other security measures or security training because they think that having MFA makes them immune to phishing attempts.
However, there are various ways that the multiple factors could be also vulnerable to phishing attacks and make you still vulnerable to succesful phishing attacks, the recent Uber security incidents and Reddit incidents are two good examples of it. Take the security breach for Uber as an example, though the compromised Uber account was protected with multi-factor authentication, the attacker allegedly used an MFA Fatigue attack and pretended to be Uber IT support to convince the employee to accept the MFA requests so that they could launch a successful phishing attack.
Limitation 2: MFA could be bypassed, even for the matured vendors
Many MFA vendors claim that their MFA solutions are well-configured to prevent unauthorized authentication. In reality, there is no one-size-fits-all MFA solution to preventing unauthorized authentication. Many MFAs are still vulnerable to multiple methods of circumventing authentication security. Here are some common MFA bypass methods that has been used in the wild to bypass MFA
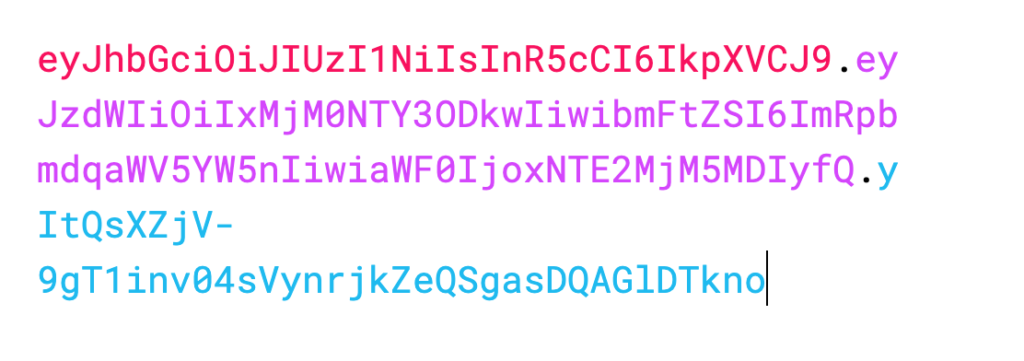
1. AitM Phishing or Use of transparent reverse proxies
Different from the traditional phishing attacks, AitM (Adversary-in-the-middle) phishing or use of transparent reverse proxies does something different, it automatically proxies credentials (username and password) and to the real login page and even the MFA code to the real login page if MFA is enabled. When victime completes the MFA through the login page, the web page completes the login session and steals the session cookie through the proxy. Once the attacker gets the session cookie, the attacker could login and bypass the MFA by making requests with the session cookie directly..
According to Proofpoint, the use of transparent reverse proxies (TRPs) are growing popularity as more and more toolkits are available on the market, for such as, Evilginx2,
2. Authentication code or OTP interception via email or SMS
SMS, Email based MFA or other OTP based MFA are popular MFA solutions used in security due to their simplicity. However, the authentication code could be intercepted by hackers through various ways. From the traditional social engineers to the most recent OTP interception bot, an attacker shows how largely authentication code could be intercepted and used to bypass MFA.
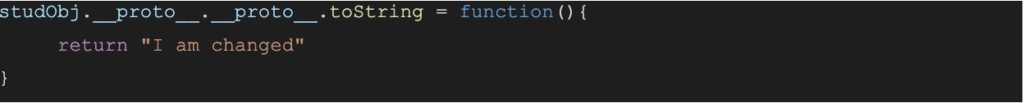
Limitation 3: MFA protection could be useless due to flaws in pages that handle it
In many instances, the improper MFA implementation in your application allows hackers a way to get around the MFA authentication. Below are some cases where MFA could be bypassed due to flaws in MFA implementation.
Lack of rate limit control leads to brute force
The MFA authentication code or OTP code is typically 4 or 6 digits long. A hacker may use brute force to obtain the right OTP code if the application’s rate limit restriction was ineffective.
Here are a few disclosure from hackerone
Bypass Slack Two Factor Authentication using Brute Force and Bypass Ubiquiti 2FA using Brute Force.
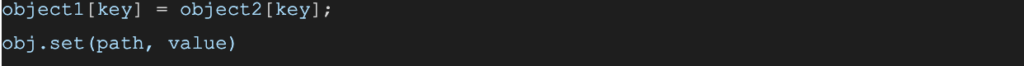
Buggy MFA implementation leads to MFA bypass
MFA protection may be useless if the authentication code verification is faulty. These are a few instances of improper MFA implementation that I have observed during penetration testing and learning from some public disclosure
An authentication code from a different user could be used by another user
For instance, after logging into his own account, an attacker may obtain a valid OTP token for himself and use it to overcome MFA by authenticating the victim.
A prior session’s authentication code could be used repeatedly.
Another frequent occurrence is the persistence of an authentication token created for a previous session after use. That implies that the MFA may be defeated if an attacker obtained any earlier authentication code.
Logic Error for MFA code verification
A public disclosure about 2FA bypass shows a 2FA was bypassed when an user send an empty authentication code to the server
The situations just stated are but a few; in my opinion, there are many more implementation errors contributing to the failure of MFA.
Limitation 4: Email and SMS based MFA are not really sufficient
One misconception about MFA is that the security effects of various MFAs are the same because they all add extra layers of factor during authentication to protect account login. Because of this misunderstanding, many businesses opt for the most convenient method to implement, such as SMS or Email tokens as their MFA methods.
The fact is that some are fundamentally more secure than others, while others are more practical. The graphic below could be used to show the various security effects of the most popular MFA technique. The weakest MFA methods are email-based and SMS-based MFA
Because an email address is not linked to a particular device, email based 2FA is the least secure of all methods. It is simple to obtain the authentication code from your email inbox because many MFA bypass methods presumptively involve email account breach for the victim. Besides Email based MFA, many security researches also show that using SMS based MFA could impose another risk factor for your organization.
Potential Methods to enhance your MFAs
MFAs have their limitations, but there are things we can do to lessen the effects of these restrictions.
- Improve Security Awareness Training
- Avoid using SMS or email-based MFA and opt for key-based MFA, is possible
- Enforce Secure SDLC when implementing your own MFA
- Ensure the MFA has a throttle or account lockout method enabled
- Regularly audit your MFA login logs
Conclusion
Setting up MFA is still the best thing you can do to safeguard your account login, despite the limitations it has. But It is crucial to be aware of the limitations of MFA and to remember not to completely rely on its security whether you use it from a reputable provider or apply it yourself.